There has been a fundamental shift in the way software vendors do business in the past few years. They’ve moved away from shipping physical software to providing their products online as SaaS (software-as-a-service) tools. For customers, this means that their software of choice is always available, and, as a bonus, they don’t need to perform any manual updates.
But this change also means that SaaS companies gather, store, and work with vast amounts of customer data. Unfortunately, this exposes both the business’s and customers’ data to security risks. Because of this, your employees should know how to keep data safe.
In this post, we’ll show you how to train your employees effectively on data protection practices.
Why Should You Train Employees on Data Protection Practices?
We’ve already mentioned the risks your data is exposed to. But how significant are they? Well, there were more than 4,100 data breaches that the public knew of in 2022. That equates to more than 22 billion records that have been exposed.
When it comes to these data breaches, some of the most common causes of data breaches are:
- Weak and stolen credentials
- Phishing and malware
- Social engineering
- User errors
- Hacking
When looking at these causes, did you notice something? The first four all apply to your employees. Yes, they’re a major point of failure in your security posture. Fortunately, if you provide proper training, you can eliminate these risks and focus on preventing the ones that aren’t up to you at all (e.g., hacking).
And when a data breach occurs, the consequences can be devastating. For instance, under the GDPR, you can face fines of up to €20 million when data breaches happen.
How to Train SaaS Employees on Data Protection Practices
Now that we’ve seen why you should train your employees in data protection practices, let’s look at the steps you should follow!
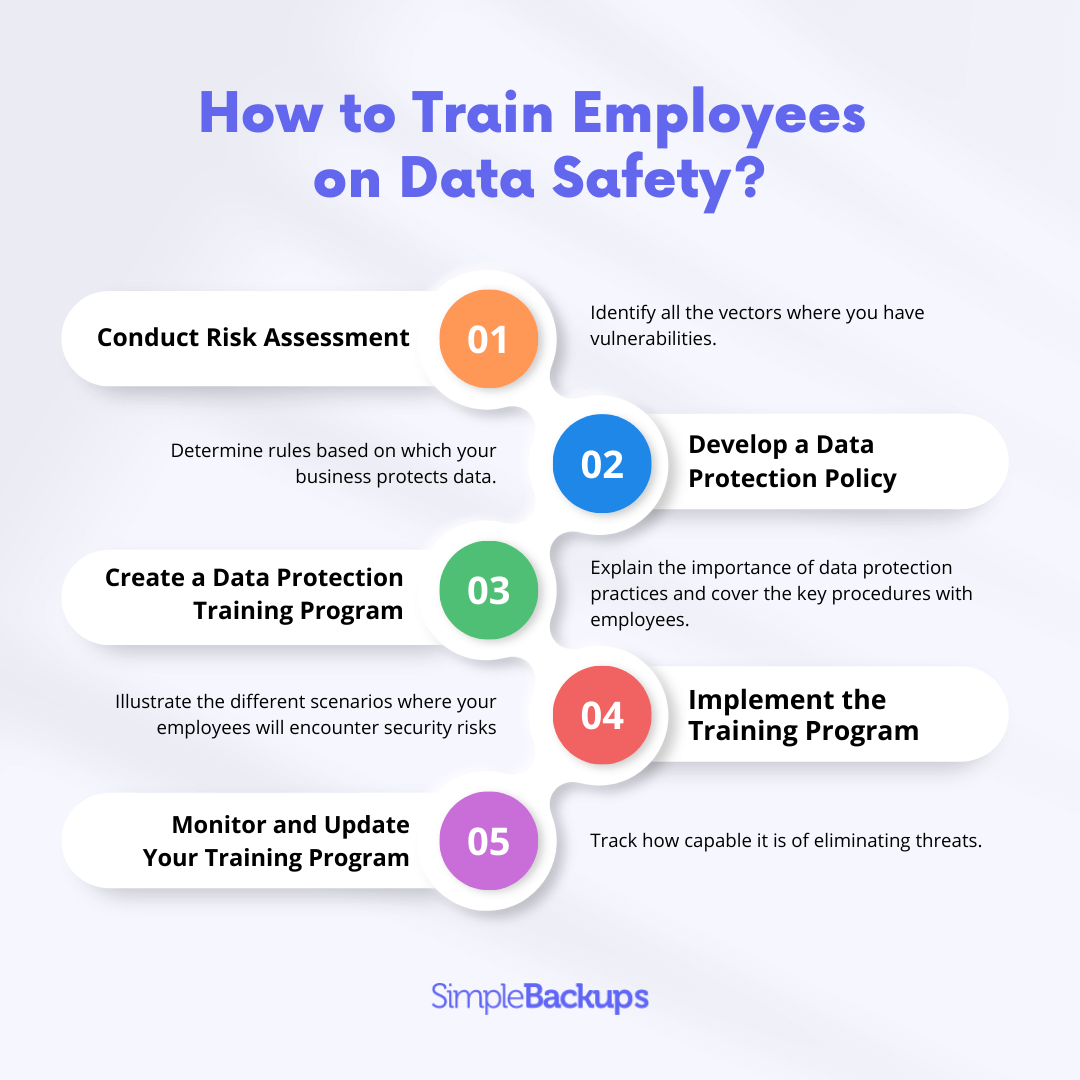
Step 1: Conduct a Risk Assessment
Your first step would be to conduct a proper risk assessment. During this process, you’ll identify all the vectors where you have vulnerabilities. This means all the departments and employees that handle customers’ data or partake in data processing activities. Similarly, identify your system risks. For example, if you use legacy software, your risk could be higher.
Step 2: Develop a Data Protection Policy
Next, based on your risk assessment, you should develop a data protection policy. It’s a set of rules and guidelines that determines how your business protects data.
While there’s no set format for these policies, you should ensure that it provides all the relevant data protection rules as well as procedures your employees should follow when working with data.
The rules and procedures you include in your data protection policy, should be:
- Appropriate for your business, considering its size, processes, and culture.
- Possible to implement in your business.
- Easy to understand and implement for your employees.
- Reviewed where necessary.
Depending on your risk vectors and particularly vulnerable areas, you might create dedicated data protection policies. For example, your Sales team may have a policy different from your Engineering team because they’ll work with customers and their data while your Engineering team will likely focus on product development and, by implication, sensitive internal data.
Step 3: Create a Data Protection Training Program
Based on your risk assessment and your data protection policy, you’ll be able to create a training program to train the appropriate employees in data protection practices.
This program should explain the importance of data protection practices and cover the key procedures with employees. It should also be simple enough so that it’s easy to understand. When it is, you’ll equip your employees with an understanding of the key concepts of data protection and what they can do to eliminate security risks. Finally, don’t forget to ask for feedback so that you don’t miss any crucial steps.
Step 4: Implement the Training Program
Once you’ve developed your training program, you can implement it. Here, it's always a good idea to use practical examples. This will illustrate the different scenarios where your employees will encounter security risks and how they need to deal with these different situations.
For example, walk them through a typical social engineering scenario. Your Finance team may get an invoice from an email address that looks like it comes from your well-known customer. Which steps should they take to verify legitimacy? Which processes can you implement to automate the verification?
This practical training instills far more knowledge than a purely theoretical approach. Keep in mind, though, that you can use some training materials available online to bolster your practical training with the necessary theory.
Step 5: Monitor and Update Your Training Program
When you’ve implemented your training program, you should consistently monitor and update it. This needs to happen for a few reasons. For instance, when monitoring the program and how your team implements it, you might find some aspects your team struggles with. You’ll then update these aspects.
Also, by monitoring your program, you’ll track how capable it is of eliminating threats. And, as new threats surface, you’ll be able to address them before they can endanger you. This is especially important as the cybersecurity landscape evolves.
What to Avoid in SaaS Data Protection Training
When creating and implementing your data protection training, there are some things you should avoid. For example, you should:
-
Understand that there’s no one-size-fits-all approach. Customize the training for your company and individual members of your team to keep everyone engaged on the highest-priority risks.
-
Ensure that the training is engaging and interactive. For instance, when you use a practical training style, as we mentioned earlier, your employees will be more engaged in the learning process.
-
Avoid overloading employees with too much information. In fact, studies have proved that people retain information better when they receive it in smaller chunks.
- You can rather spread out your training program over several sessions.
- You can also provide training on the basics to your entire team, and then teach specific members more advanced topics based on their functions.
-
Avoid not monitoring and updating your program based on how it's implemented or as your needs evolve. This will ensure that your training remains effective and that your team eliminates security risks as far as possible.
Keep Your Own and Your Customer’s Data Safe!
Keeping your business’s and its customers’ data safe in a world where data breaches are becoming increasingly prevalent is hard. One of the best ways to prevent the majority of security risks is by training your employees on data protection practices.
By customizing your training to the risks you’re most often exposed to and keeping your ears open for feedback, you’ll be able to stay light on your toes when it comes to vigilance and data protection!